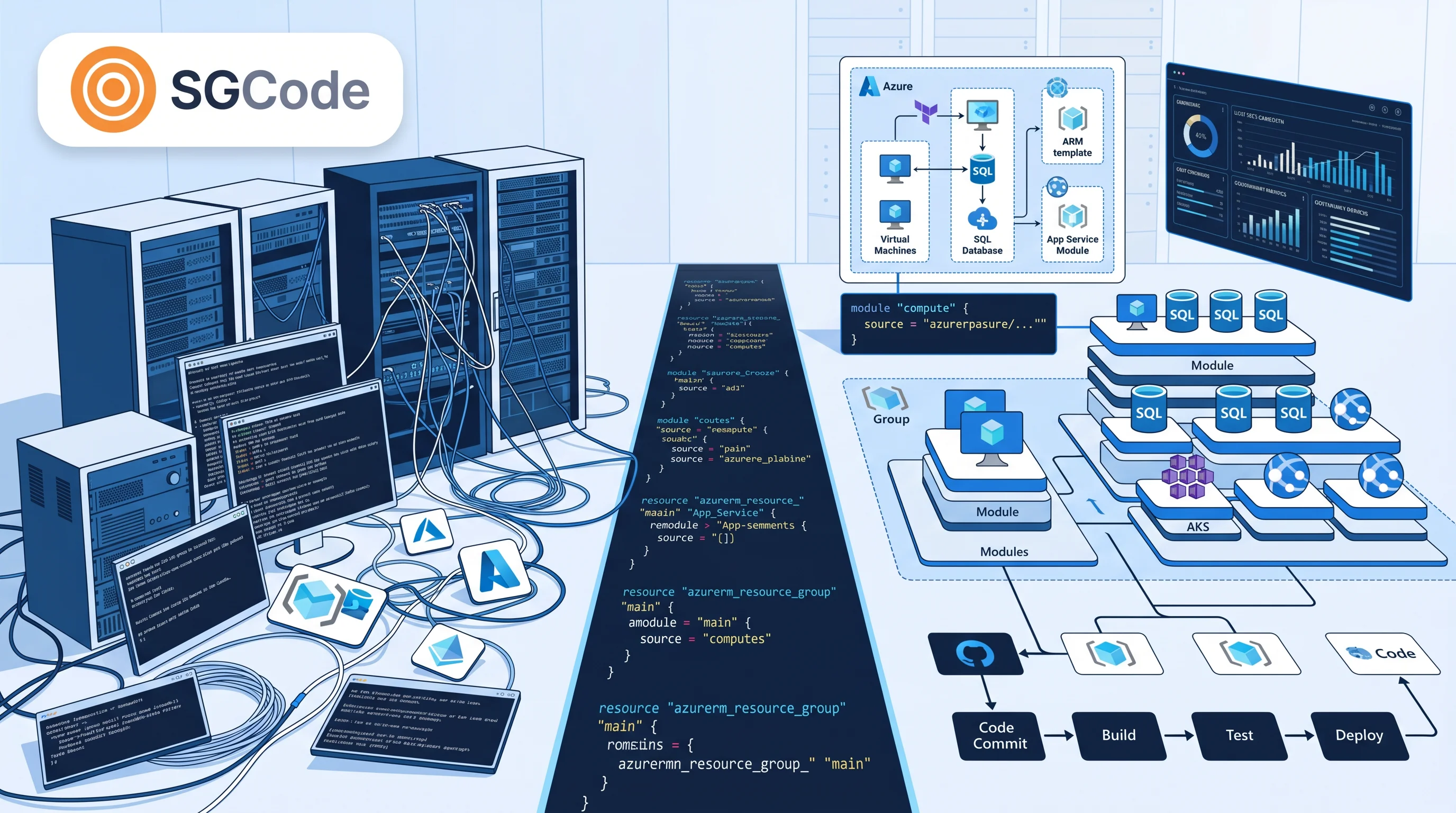
Struggling with Terraform import drift, shadow infrastructure, ClickOps backlogs, or legacy AWS/Azure/GCP resources? This comprehensive IaC Adoption Matrix guide reveals how to assess your infrastructure maturity, codify brownfield environments, eliminate configuration drift, and achieve 100% IaC coverage using SGCode, StackGuardian's automated Terraform/OpenTofu generator.
Whether you're battling terraform import challenges, orphaned tfstate files, or manual console provisioning, the IaC Adoption Matrix provides a systematic framework for legacy infrastructure codification. Learn technical remediation for all 9 scenarios, tackle common IaC migration pitfalls, and deploy SGCode's Infra2Code for AI-powered discovery and code generation.
This guide provides technical depth for every scenario, addressing migration backlogs and demonstrating how SGCode automates codification across AWS, Azure, and GCP - making it the ideal resource for DevOps engineers, platform teams, and cloud architects seeking solutions for "ClickOps to IaC," "Terraform brownfield migration," or automated AWS IaC adoption.
Why IaC Adoption Matters in 2026: Ending ClickOps Forever
Manual "ClickOps" creates IaC backlogs that kill engineering velocity:
- Reverse-engineering hell: Months parsing CloudTrail logs or Azure Activity Logs for undocumented resources.
- Configuration drift: terraform plan outputs massive diffs from ad-hoc console changes.
- Shadow IT risks: Untracked S3 buckets, IAM roles, or Kubernetes clusters bypass security scans.
- Orphaned state silos: tfstate files with stale resource addresses block terraform apply.
Organizations with full IaC coverage achieve:
- 90% faster provisioning via GitOps workflows
- 70% incident reduction through drift detection
- Instant compliance with OPA policies and guardrails
The IaC Adoption Matrix—a 3x3 diagnostic grid—maps your Terraform state, cloud resources, and HCL code to reveal gaps and prescribe fixes.
The IaC Adoption Matrix: 9 Detailed Scenarios with Technical Remediation
The matrix evaluates:
- IaC Code Present? → HCL/Terraform .tf files in Git
- Cloud Resources Exist? → Live inventory via AWS CLI, Azure CLI, gcloud
- State File Exists? → terraform.tfstate (local/remote backend)
Scenario 1: No IaC, No Resources, No State (Greenfield)
Symptoms: Empty AWS account (aws ec2 describe-instances → []), no .tf files, no terraform.tfstate.
Risks: Clean slate—no issues.
Fix: Bootstrap IaC-first. Create modular VPC (aws_vpc.main, for_each subnets), S3 backend with DynamoDB locking:
text
terraform {
backend "s3" { bucket = "my-tfstate" key = "prod/terraform.tfstate" dynamodb_table = "tf-locks" }
}
SGCode: Generates org-style Terraform/OpenTofu scaffolds matching your naming conventions.
Scenario 2: No IaC, Resources Exist, No State (Shadow Infrastructure)
Symptoms: 50+ EC2s/RDS via aws resourcegroupstaggingapi get-resources, no HCL/tfstate. Console sprawl.
Risks: Zero visibility—terraform plan impossible; CloudTrail shows CreateInstance API calls sans versioning.
Fix: Discovery tools (Former2, Terraformer, SGCode) → HCL export. Init empty state, batch import:
terraform init
terraform import 'aws_instance.web[*]' 'i-1234567890abcdef0'Prioritize: prod (Environment=production tags) → dev. Handle circular deps with -parallelism=1.
Scenario 3: No IaC, No Resources, State Exists (Impossible State)
Symptoms: tfstate holds aws_s3_bucket.example but bucket deleted via console.
Risks: terraform plan fails: "resource not found"; poisons future imports.
Fix: terraform state rm aws_s3_bucket.example or rm terraform.tfstate. Purge S3 backend objects.
Scenario 4: No IaC, Resources Exist, State Exists (Legacy + Orphaned)
Symptoms: tfstate tracks VPC but misses EC2s; resources live.
Risks: Hybrid drift—state show partial; scaling blocked.
Fix: Extract: terraform state show aws_vpc.main > vpc.tf. Full re-import: terraformer import aws --resources=ec2,vpc. SGCode auto-generates complete modules.
Scenario 5: IaC Present, No Resources, No State (Defined but Unused)
Symptoms: main.tf defines aws_eks_cluster but no EKS exists.
Risks: Untested code—stale ARNs, provider mismatches.
Fix: terraform init && validate && plan && apply. Add remote state.
Scenario 6: IaC Present, No Resources, State Exists (Stale State)
Symptoms: HCL + tfstate, resources cost-cut manually.
Risks: Infinite destroy/create loops in plan.
Fix: terraform apply -refresh-only or state rm orphans, then re-apply.
Scenario 7: IaC Present, Resources Exist, No State (Unmanaged Infra)
Symptoms: HCL + drifted live ASG/EC2, no tfstate.
Risks: Console overrides HCL—drift snowballs.
Fix: Sequential import: VPC → subnets → instances. Post-import: plan reveals diffs.
Scenario 8: Fully Managed IaC (Ideal State)
Symptoms: terraform plan → "No changes".
Risks: Complacency—drift possible.
Fix: GitOps PRs with OPA/Sentinel; CI plan + auto-apply green plans.
Common Challenges: Tackling IaC Backlogs
Legacy infra creates vicious cycles:
- Shadow Infrastructure (No IaC, resources exist): Undiscovered EC2s or VMs accumulate, fueling drift backlogs.
- Orphaned State: Leftover tfstate files mismatch reality, complicating audits.
- Drift Backlogs: Post-IaC, manual changes create reconciliation queues.
- Complex Dependencies: Real-world apps (e.g., 500 EC2s as clusters, not singles) overwhelm manual coders.
How SGCode Solves IaC Migration
SGCode (StackGuardian's code platform) operationalizes the matrix:
Core Capabilities
- Automated Discovery: Scans AWS, Azure, GCP for resources, relationships, and context.
- Intelligent Code Generation: Produces Terraform/OpenTofu matching your modules, naming, and patterns—not generic dumps.
- State Automation: Generates tfstate files; no manual imports.
- Drift Detection: Activates immediately post-conversion.
- Governance Integration: Policies, guardrails from day one.
Features:
- AI Pattern Recognition: Groups 500 instances into 12 dev machines, 8 clusters, 3 DB tiers.
- Style Matching: Analyzes your repos for seamless integration.
- Template-to-Workflow: Reusable modules + state management = platform, not export.
Real Impact:
- Time Savings: Weeks vs. 12-18 months building in-house.
- Risk Reduction: Eliminates drift incidents.
- Battle-tested in GxP/pharma/healthcare enterprises and global cloud teams.
Step-by-Step: Using the Matrix with SGCode
- Assess: Run matrix on accounts. E.g., Shadow IT? Prioritize discovery.
- Codify: SGCode's Infra2Code scans → generates code/state → PRs with policies.
- Reconcile Drift: Auto-import unmanaged resources.
- Scale: Enforce PR guardrails; monitor backlogs.
- Greenfield: IaC-first for new projects.
Clears backlogs 10x faster than manual Terraform imports.
Best Practices for Full IaC Coverage
Drawing from Terraform at scale playbooks:
- Start Small: Pilot one account with matrix.
- Match Org Style: Use SGCode's analysis.
- PR Workflows: Enforce reviews/guardrails.
- Multi-Cloud: AWS/Azure/GCP unified.
- Backlog Grooming: Weekly drift scans.
Avoid pitfalls: Don't ignore state mismatches—reconcile early.
Conclusion: From Legacy to IaC Mastery
The IaC Adoption Matrix demystifies migration, while SGCode delivers the automation. Codify legacy infrastructure today—eliminate backlogs, boost governance, and focus on growth.
Ready to remove ClickOps?
FAQ: IaC Codification, ClickOps, and SGCode
What is the IaC Adoption Matrix?
A 3x3 grid assessing IaC code, live resources, tfstate to diagnose maturity and prescribe Terraform import, drift fixes, or greenfield starts.
How do I convert ClickOps to IaC?
Use discovery (SGCode/Terraformer) → generate HCL → terraform import → PR workflows. SGCode automates all steps.
What is configuration drift and how to fix it?
Live resources diverge from tfstate/HCL. Fix: terraform plan, import diffs, enforce GitOps. SGCode detects/prevents instantly.
What is SGCode?
StackGuardian's platform for automated Terraform/OpenTofu generation from cloud resources. Features Infra2Code AI grouping, style matching, state mgmt, drift detection.
How does SGCode handle complex legacy infra?
AI recognizes patterns (EC2 clusters, not singles), matches your modules, generates reusable templates + tfstate.
Terraform import vs. SGCode?
Manual import = weeks of deps/conflicts. SGCode = minutes, production-ready code with governance.
Can SGCode handle AWS, Azure, GCP?
Yes—multi-cloud discovery, Terraform/OpenTofu output, unified workflows.
Is SGCode suitable for enterprises?
Built for GxP/pharma scale; policies, PR guardrails, battle-tested compliance.