Cloud security is a top concern for every organization that operates or moves to the cloud. Data breaches and misconfigurations can have serious consequences. How can teams keep up with evolving threats while managing complex and distributed cloud environments?
StackGuardian offers an AI-powered infrastructure automation solution. It is a cloud orchestration platform designed to help organizations enforce security, maintain compliance, and streamline operations. This blog explores cloud security best practices and how StackGuardian can help you strengthen your security and compliance postures.
Cloud Security Implementation Challenges
Cloud adoption, global expansion, and distributed architectures bring new risks that organizations must address at scale. Let’s take a look into a few of the most common cloud security challenges for enterprises:
- Misconfigurations and Human Errors: Simple mistakes in cloud settings can expose sensitive data to the public or leave systems open to attack. Misconfigurations are one of the leading causes of cloud security incidents.
- Complex Multi-Cloud and Hybrid Setups: Enterprises increasingly use multiple cloud providers and hybrid architectures to meet business needs. While this approach offers flexibility and scalability, it also expands the attack surface. Each new service or integration adds more entry points for attackers.
- Visibility is a challenge: Many teams struggle to monitor assets and activity across various cloud and on-premises systems, making it difficult to spot threats or misconfigurations. The dynamic nature of cloud environments, combined with the large volume of data generated, makes effective observability implementations challenging. Without centralized dashboards and advanced analytics, organizations risk missing critical security events or failing to respond quickly enough to incidents.
- Regulatory compliance is complex. Different regions and industries have unique rules. Keeping up with evolving requirements is difficult, especially across multiple hybrid environments. Organizations must continuously map their controls to evolving standards, such as GDPR, HIPAA, and ISO 27001. The lack of unified compliance tools across providers can make it difficult to ensure consistent enforcement and reporting.
- Insider Threats and Shadow IT practices: When staff use unapproved software and services, they can create blind spots and increase the risk surface for enterprises. Even more, employees or contractors with elevated access privileges may intentionally or accidentally compromise data.
Cloud Security Best Practices
How can organizations reduce their risk and improve security in the cloud then? By adopting proven best practices that aim to enforce control, guardrails, observability, and automated remediation.
Implement Robust Identity and Access Management (IAM)
A well-planned and executed identity and access management is critical to set up a foundational basis for security in the cloud. Aim to apply the principle of least privilege as much as possible and grant users only the access they need for their roles. Set up processes to review permissions regularly and update them accordingly. Always prefer IAM roles and temporary credentials instead of static and hard-coded or long-lives secrets and keys. Enable multi-factor authentication for human flows, especially for those with elevated privileges. To simplify management centralize IAM with single sign-on integrations.
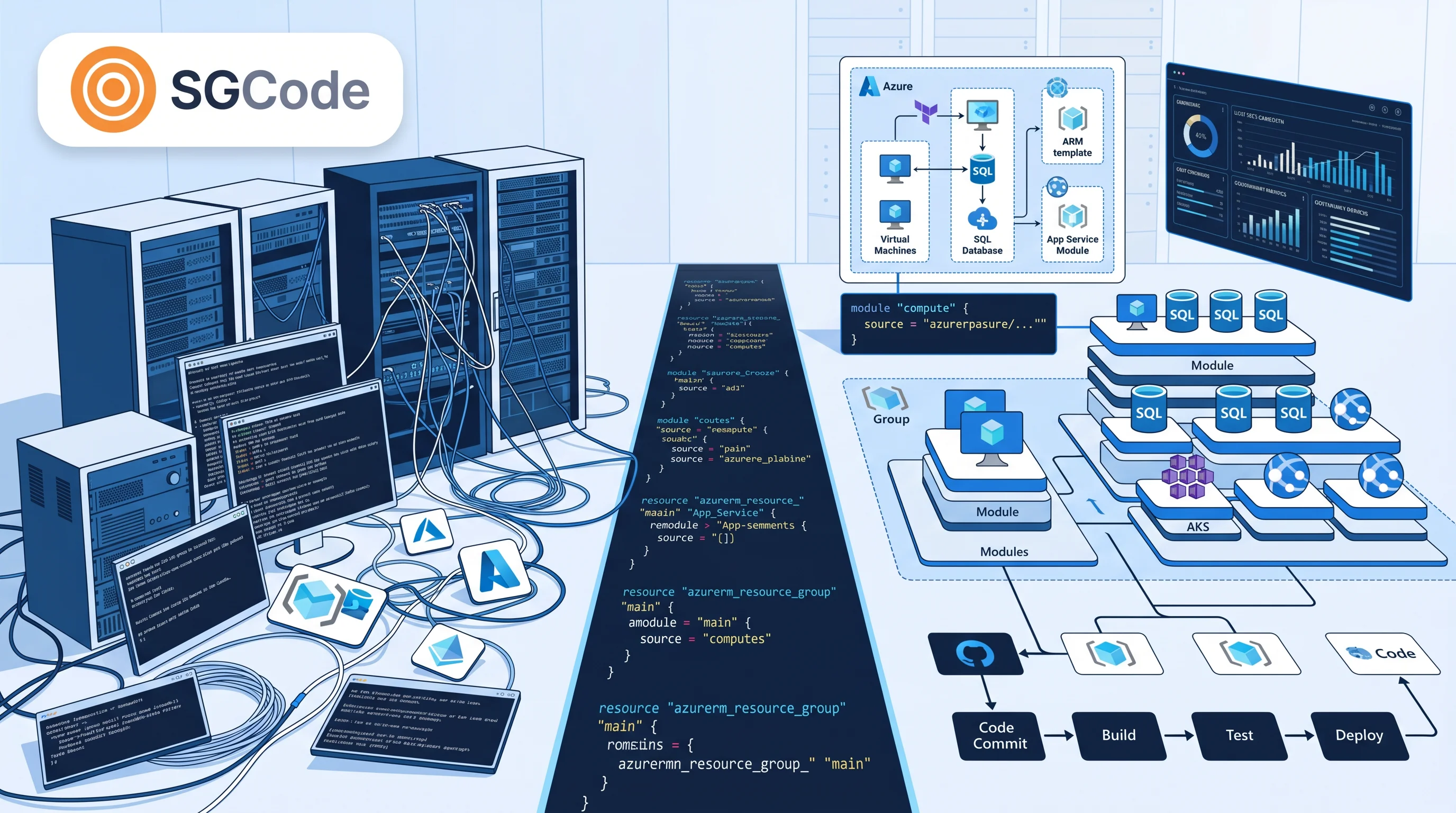
Configuration and Automation
Configure and manage resources only with Infrastructure as Code (IaC) in order to enforce secure configurations at scale. After provisioning, scan IaC templates and cloud environments for misconfigurations continuously. Automate security patching to reduce manual effort and minimize exposure. Where possible, adopt serverless technologies that abstract the underlying infrastructure, effectively offloading many of the security considerations back to your cloud provider.
Observability
Another critical component of secure cloud setups is a well-architected observability strategy that leverages the right tools. To achieve optimal observability and monitoring implementation, centralize logging and monitoring from all systems, cloud services, and on-premises infrastructure in one place for easier analysis. Enable tools that log all activities and API calls to maintain a complete audit trail of actions while blocking anyone from tampering these logs. Customize monitoring dashboards for real-time visibility, while setting up meaningful alerts that notify you when things go wrong. AI-enabled observability and anomaly detection are also becoming increasingly common, helping organizations spot unusual activity quickly.
Governance & Compliance
In order to comply with regulations you need governance and controls in place for your cloud environments. Define security baselines and use tools to enforce policies for all infrastructure resources. Map controls to the compliance frameworks you need such as ISO 27001, SOC 2, and GDPR to meet compliance requirements. As these regulations aren’t static, regularly review controls and update them.
Data protection
One of the most valuable resources of modern organizations is their proprietary data. To protect your data, start by classifying your different datasets and data sources based on their criticality and confidentiality. Encrypt any sensitive data in transit and at rest to prevent unauthorized access or data leaks. Another critical component of data protection is how you handle secrets and keys. Store your secrets in dedicated secrets managers or vaults, not in your software and infrastructure code and configuration files in plain text. As failures of IT systems occur occasionally, automate regular backups and test your disaster recovery processes to ensure data can be restored after an incident within an acceptable timeframe.
How StackGuardian Can Help Your Cloud Security Posture
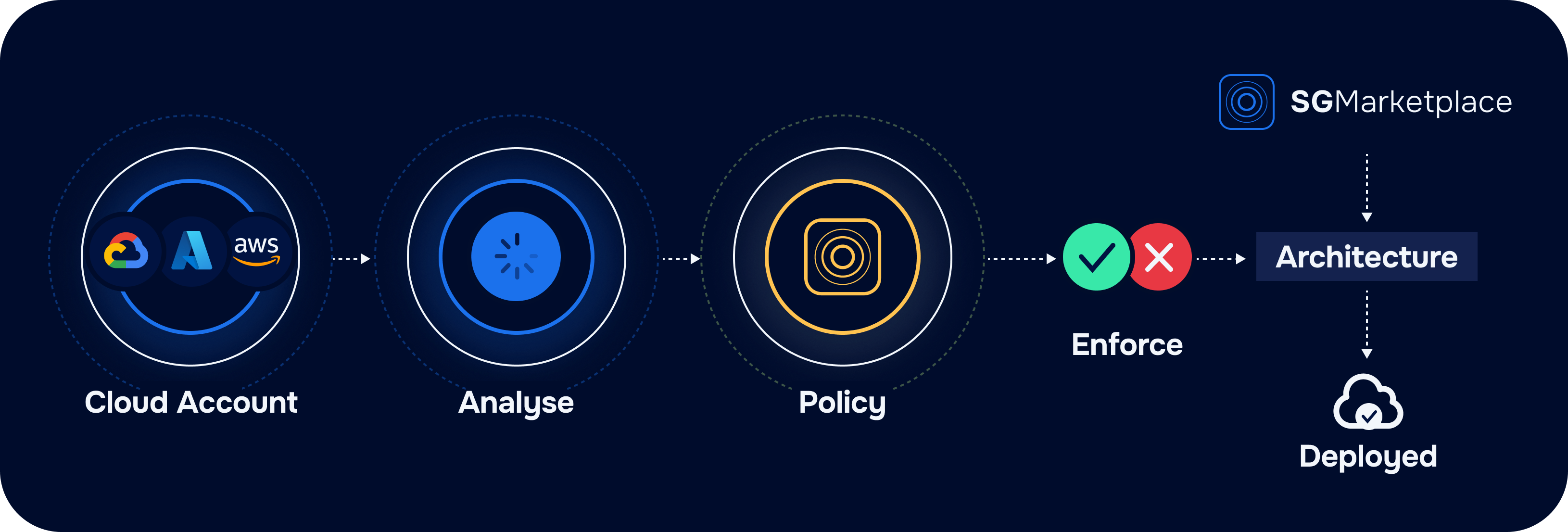
How do you enforce security best practices, maintain compliance, and manage risks at scale? StackGuardian provides a set of features to help organizations address these challenges directly.
Policy Development Made Easy
StackGuardian’s no-code policy builder enables you to define security guardrails without writing code. You can create policies that apply organization-wide, target specific teams or environments.
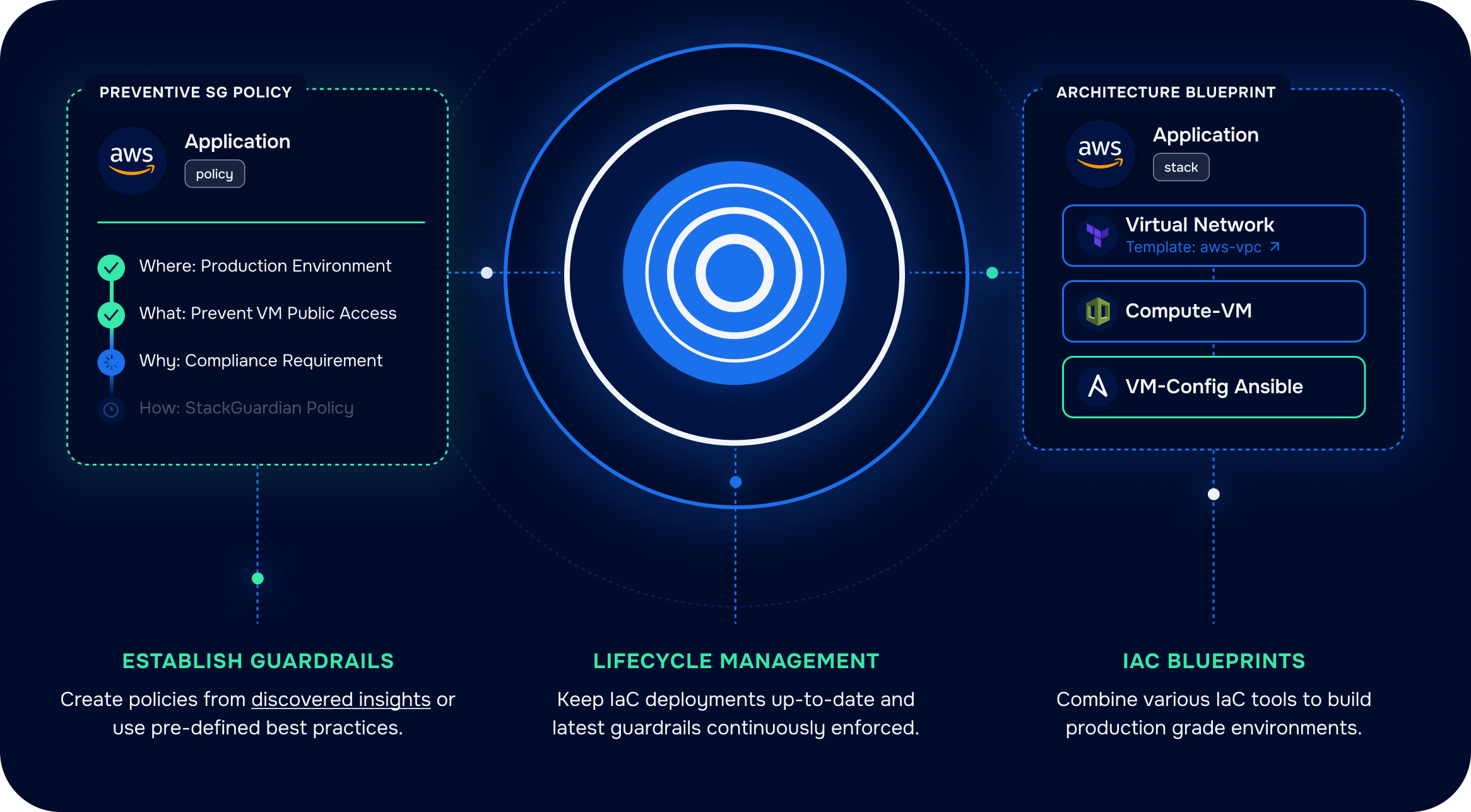
Use the “Provide Guardrails” feature to enforce security baselines, such as requiring encryption for all sensitive data storage or enforcing tagging standards. Policies can be activated to automatically block non-compliant deployments, require approval, notify users and by that ensuring that best practices are followed every time.
Benchmarking Security Postures
In order to ensure your cloud environment meets industry standards, StackGuardian offers built-in benchmarks for frameworks like CIS, NIST, PCI DSS, SOC 2, and GDPR among others.

The platform also supports custom benchmarks, allowing you to define checks tailored to your unique business or regulatory needs. You can apply these benchmarks to AWS, Azure, and other cloud accounts, and get reporting and visibility on compliance status and areas needing improvement.
Real-Time Security and Compliance Insights
Visibility is key to effective cloud security. StackGuardian’s dashboards provide real-time insights into your security and compliance posture.

The Compliance Dashboard highlights failed checks by cloud, severity, and account, helping you quickly identify and address gaps.

The Security Dashboard summarizes vulnerabilities, shows trends over time and pinpoints the most common issues in your environment. These tools support continuous monitoring and faster response to risks.
Secure Secrets Management
Managing credentials and API keys securely is critical. StackGuardian offers a secure vault system to store secrets in an encrypted, centralized location.

You can use StackGuardian Vaults or connect to third-party solutions like HashiCorp Vault and Azure Vault. This approach ensures that sensitive data is never hardcoded or exposed, and access is tightly controlled.
Drift Detection and Consistent Configurations
Configuration drift can lead to security gaps. StackGuardian tracks the state of your resources in a workflow and detects drift from your intended configurations. The platform provides details on drifted resources, the last time they were detected as drifted, and upcoming checks, making it easier to maintain a consistent and secure environment.
Flexible Workflows for Any Cloud Stack
StackGuardian supports a wide range of workflow and tooling options, including Terraform, Opentofu, Ansible, CloudFormation, Helm, Kubectl, but also custom workflows. Within each workflow, you can enforce compliance checks, view policy results, and monitor resource drift. This flexibility allows you to integrate StackGuardian into your existing DevOps processes and manage security across different cloud stacks.
Conclusion
Cloud security is a continuous effort. Risks evolve as cloud environments grow and change. Are your current processes enough to keep up? StackGuardian brings automation, visibility, and control to your cloud operations. It helps you enforce best practices, maintain compliance, and respond to threats faster. With no-code policy tools, real-time dashboards, and secure secrets management, StackGuardian supports teams at every stage of cloud adoption.
Book a demo today!